Mobile application security assessment solution discovers and expedites malicious and potentially risky actions in your mobile applications on both Android/IOS, keeping your business and customers secure against attacks. Snappy Code Audit has carried out numerous penetration testing engagements on mobile applications from various horizons such as:
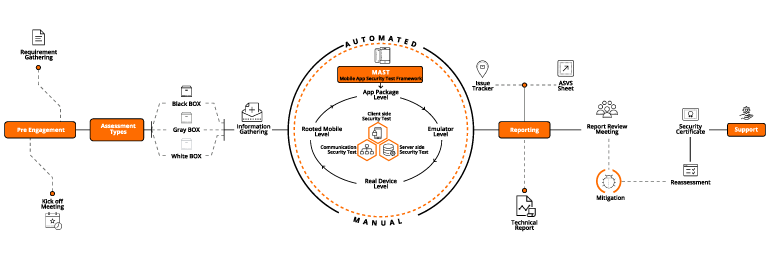
At Snappy Code Audit, we combine multiple assessment tools like automated scans and combined-depth manual tests to get the most comprehensive security assessment of the client applications.
Snappy audit tool is one of the top rated security testing tools available in market. We provide java static analysis tools, static code analysis tools java , code review tools for helps to ensure applications are developed and managed securely.
Static code investigation devices java filters byte code for alleged bug example to discover surrenders as well as suspicious code. In spite of the fact that Findbugs needs the aggregated class documents it isn’t important to execute the code for the investigation. Working with Findbugs keeps from delivery avoidable issues. It is likewise an astounding inspiration for enhancing the aptitudes of improvement groups to compose better code in any case.
So our tool java static analysis tools helps to save your time and your work will done smoothly.
Creates a threat profile that lists all your applications’ risks and enables testers to replicate relevant attacks rather than using random attacks like SQL injection, cross-site scripting, and session hijacking.
Tests apps such as mobile banking, e-commerce and mobile payment systems on various device platforms under a single program including iPad, iPhone, Android in an unified plan for improving efficiency.
Access our dedicated team of mobile application security researchers to stay on top of the latest threats and trends in the mobile app world and enable predictive intelligence in app security.
Because:
